
Creating a Voluntary Data Sharing Program Between The Government and the Private Sector (S. 754)
Do you support or oppose this bill?
What is S. 754?
(Updated June 19, 2019)
In hopes of bolstering the nation's cyber security, this bill attempts to woo private sector companies into sharing computer data with the federal government by offering those companies expanded liability protections when they give up data.
The participation of private entities — typically businesses — would be completely voluntary, and they would face no liability for non-participation. Private entities also would have limited liability for monitoring their consenting consumers networks — and they could share cyber threat information that has personal consumer information removed first.
All monitoring of a private entity’s network and cyber threats against that network must be done with the user’s consent.
On the federal government's end, this bill would require the Director of National Intelligence (DNI), the Secretary of Homeland Security (DHS), the Secretary of Defense (DOD), and the Attorney General (DOJ) to work together to develop new cybersecurity procedures.
Information about threats would be sent to the Department of Homeland Security (DHS), which could then be shared in real-time with other federal agencies as needed. These procedures would promote more seamless sharing of classified and unclassified cyber threat indicators across federal agencies. For those of you who don't know, Cyber threat indicators are the measures that help spot the malicious gathering (active or passive) of data, security vulnerabilities that exist or are being exploited and defeated, and the exfiltration of information.
Interim policies and procedures must be created within 60 days of this bill’s enactment, and final policies and procedures need to be established within 180 days. Once both the interim and final policies are developed, they would be submitted to Congress for review and made public.
The final guidelines would have to limit the impact on privacy and civil liberties for activities conducted by the federal government. In addition to preventing the inclusion of personal information when cyber threat indicators are shared, the final guidelines must create a process for destroying such information that is inadvertently shared. Limitations on how long cyber threat indicators may be kept would also be included.
Argument in favor
The federal government needs to be as agile as possible in responding to cyber threats, and this bill strikes an effective balance in protecting individual’s privacy and allowing information to flow to intelligence agencies.
Argument opposed
The privacy protections in this bill are severely lacking. Requiring reports about privacy breaches every two years doesn’t convey a sense of urgency about protecting civil liberties.
Impact
Private sector entities, state and local agencies, federal agencies that manage cyber security threats, U.S. cyber security, the Director of National Intelligence (DNI), the Secretary of Homeland Security (DHS), the Secretary of Defense (DOD), and the Attorney General (DOJ).
Cost of S. 754
The CBO estimates that this bill would cost about $20 million over the 2016-2020 period, or about $4 million annually.
Additional Info
Of Note: Voluntary information sharing between private companies and federal agencies is already taking place through a program designed to help defense contractors protect themselves from cyber threats. This is done through the identification of cyber attack signatures, which can be logged and then used to guard against future attacks.
There has been substantial outcry against this legislation because of a perceived lack of privacy protections. When this legislation was passed through a 14-1 vote of the Senate’s Senate Intelligence Committee, Senator Ron Wyden (D-OR) remarked that “if information-sharing legislation does not include adequate privacy protections then that’s not a cybersecurity bill — it’s a surveillance bill by another name.”
For their part, the bill’s proponents believe the adequate safeguards for personal information are included in this version of the bill. Senator Dianne Feinstein (D-CA) has said that the “privacy provisions are substantial,” and that the amendments found in this version are an improvement on previous drafts of the bill. Those amendments have helped galvanize support for this legislation in the Senate, as it failed to receive a vote after its introduction in 2014.
In-Depth: Private entities would be authorized to have defensive measures for their own networks, and could share information with the federal government in addition to any cyber threat information. There would be no authorization for offensive or destructive activities undertaken on a private entities network.
This bill would require federal agencies to submit an implementation report to the Inspector Generals of relevant federal agencies and to Congress within one year of this legislation’s enactment. Ongoing reports would be required thereafter at least once every two years.
Media:
- Sponsoring Sen. Richard Burr (R-NC) Press Release
- Senate Intelligence Committee Press Release
-
CBO Estimate
- The Hill
- National Journal
- U.S. News & World Report
- Wired
- FCW
- International Business Times
- Center for Democracy and Technology (Opposed)
- EFF Action (Opposed)
- Engadget
Summary by Eric Revell
(Photo Credit: Flickr user x-ray delta one)
The Latest
-
 IT: 🖋️ Biden signs a bill approving military aid and creating hurdles TikTok, and... Should the U.S. call for a ceasefire?Welcome to Thursday, April 25th, readers near and far... Biden signed a bill that approved aid for Ukraine, Israel, and Taiwan, read more...
IT: 🖋️ Biden signs a bill approving military aid and creating hurdles TikTok, and... Should the U.S. call for a ceasefire?Welcome to Thursday, April 25th, readers near and far... Biden signed a bill that approved aid for Ukraine, Israel, and Taiwan, read more... -
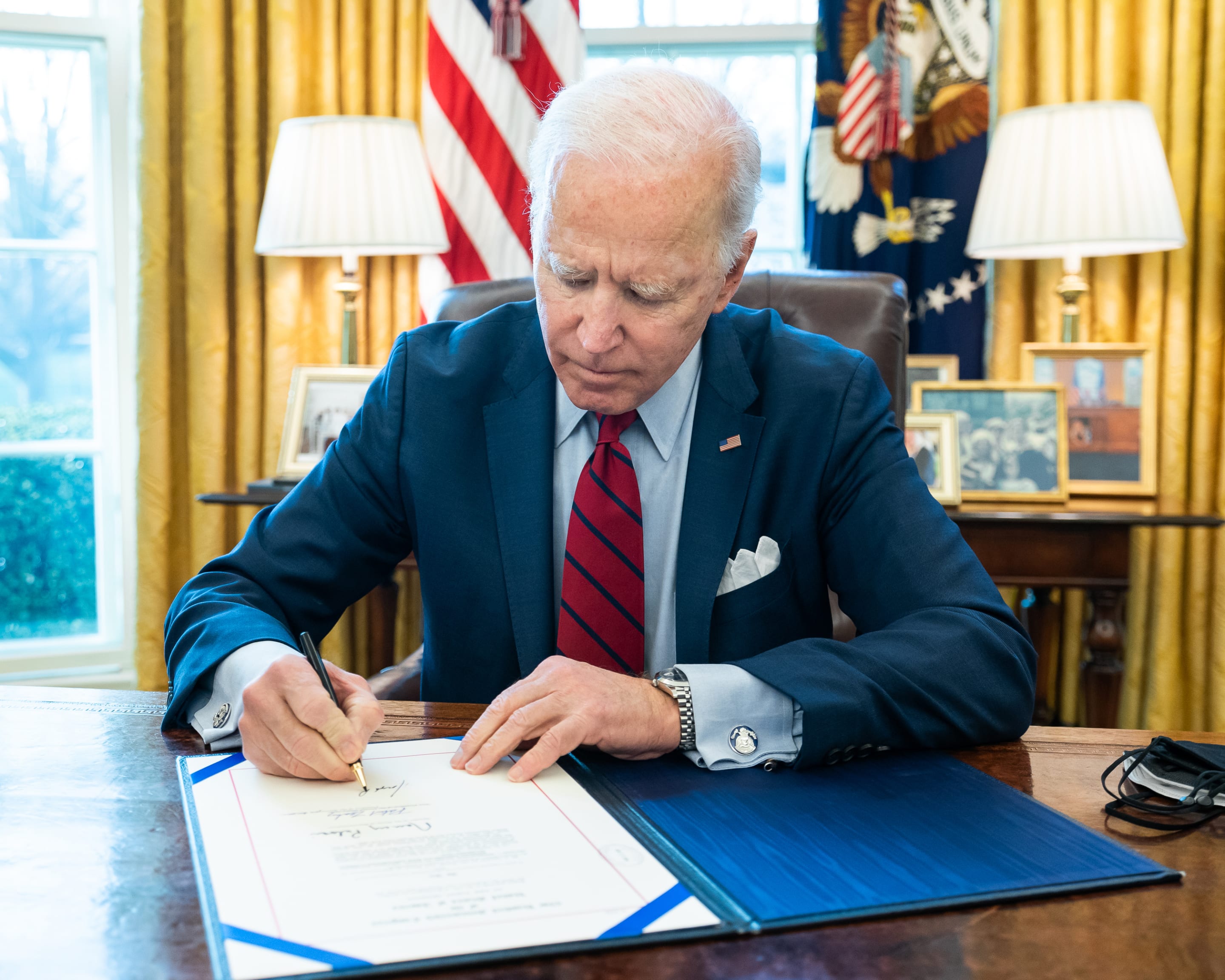 Biden Signs Ukraine, Israel, Taiwan Aid, and TikTok BillWhat’s the story? President Joe Biden signed a bill that approved aid for Ukraine, Israel, and Taiwan, which could lead to a ban read more... Taiwan
Biden Signs Ukraine, Israel, Taiwan Aid, and TikTok BillWhat’s the story? President Joe Biden signed a bill that approved aid for Ukraine, Israel, and Taiwan, which could lead to a ban read more... Taiwan -
 Protests Grow Nationwide as Students Demand Divestment From IsraelUpdated Apr. 23, 2024, 11:00 a.m. EST Protests are growing on college campuses across the country, inspired by the read more... Advocacy
Protests Grow Nationwide as Students Demand Divestment From IsraelUpdated Apr. 23, 2024, 11:00 a.m. EST Protests are growing on college campuses across the country, inspired by the read more... Advocacy -
 IT: Here's how you can help fight for justice in the U.S., and... 📱 Are you concerned about your tech listening to you?Welcome to Thursday, April 18th, communities... Despite being deep into the 21st century, inequity and injustice burden the U.S. read more...
IT: Here's how you can help fight for justice in the U.S., and... 📱 Are you concerned about your tech listening to you?Welcome to Thursday, April 18th, communities... Despite being deep into the 21st century, inequity and injustice burden the U.S. read more...
 Climate & Consumption
Climate & Consumption
 Health & Hunger
Health & Hunger
 Politics & Policy
Politics & Policy
 Safety & Security
Safety & Security
